Monitor and restart Tomcat with PowerShell
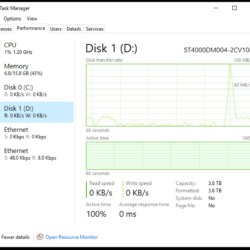
We have been dealing with a server issue on and off for the past few months where Tomcat becomes unresponsive, but still appears to be running. Traditional service monitoring wasn’t detecting the crash, but our users were. This looks bad!